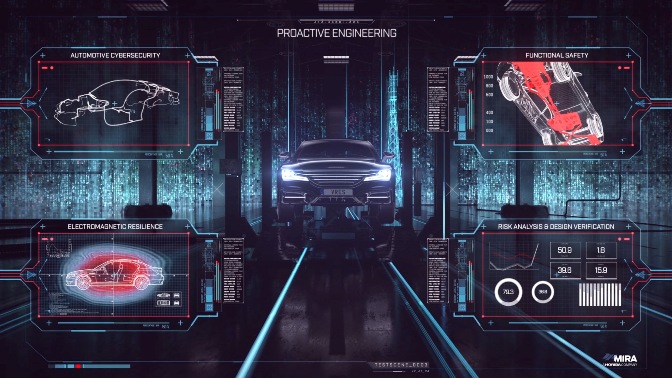
Jonathan Newell talks to HORIBA MIRA about vehicle resilience and the battle for supremacy in the cyber-security arms race
The automotive industry is barrelling along the highway towards Connected Autonomous Vehicles (CAV) and while fully connected and fully autonomous cars are still a spot on the horizon, nonetheless every new car that comes on the market offers new levels of sophistication, connectivity and autonomy at all levels.
As that sophistication increases, so does the potential threat to the security of the on-board computer systems. All computer and smartphone owners are aware of the threats that exist and mitigate against data loss with firewalls, security software and safe computing practices, but how does this translate to the vastly more complex computing environment of CAVs?
To answer that question and put context around the cybar-security of automotive products, UK automotive engineering consultancy, HORIBA MIRA, has just released a white paper “Why automotive security is different”.
To discuss it in more detail, I spoke to Anthony Martin, Head of Vehicle Resilience Technologies and Paul Wooderson, Chief Engineer of the Cyber-Security team at HORIBA MIRA.
Complexity at Pace
The white paper gives the reader some idea of how vehicles are becoming more complex as a computing environment. Internal computing power for engine management, vehicle control and external signal processing combine with Advanced Driver Assist Systems (ADAS) microprocessors and the sensor inputs that feed them. Vehicle to Infrastructure (V2x) communications take the data workflow outside the boundaries of the vehicle, connecting it to other sources of data (and threats).
In terms of the quantity of data being processed, the report forecasts that the vehicle’s sensor bandwidth alone will amount to 40Gbit/second, which equates to around 40TB of data processing for every hour of operation. Low latency 5G communications for V2x will increase this flow potentially by orders of magnitude.
In this environment, there’s clear potential for malicious activity that could compromise the operation of the vehicle. HORIBA MIRA recognised this threat early and has been working on vehicle threat resilience for a number of years.
Collaborative approach
In 2019, the “ResiCAV” project was created in partnership with other specialist organisations including the Warwick Manufacturing Group and Thales. Backed by Innovate UK, the project created an actionable environment for tackling cyber-security threats to connected vehicles. The project is now in its second phase.
According to Wooderson, the organisation has in fact been working on vehicle cyber security for 12 years. “It was initially started as a research project but its scope has increased as vehicles have become more connected. There is more potential for things to go wrong as humans come further out of the loop,” he says.
More recently, regulatory frameworks have been put in place with both UNECE and ISO/SAE standards in place. However, as Martin explains, regulations have been in development for about 5 years and are just a starting point.
“Standards are the minimum requirements and individual manufacturers take different approaches based on risk. One of our tasks is to support them and offer a consultancy, testing and assessment service,” he says.
He goes on to explain the approach HORIBA MIRA takes. “Threats are analysed at a full system level. Vehicle manufacturing isn’t like a jigsaw where the whole is made up of the sum of the parts so the product must be analysed at the top level as there are often issues around system integration,” he says.
Continuous Protection
As Martin explains, although much of the work being undertaken by the automotive industry relates to existing threats being mitigated before the vehicle leaves the showroom, consideration must also be given to future threats that may also emerge throughout the lifetime of the car.
A new regulation soon to be published examines the mechanism for providing over-the-air updates and the response to emerging threats that may affect vehicles that have left the dealership and are on the road.
One of the roles of the vehicle resilience team at HORIBA MIRA is to help the industry find its way through the new regulatory context and achieve the dual approach of security-aware design and managing the ongoing vehicle operation.
“While complete indemnity from evolving cybersecurity risk cannot be achieved, risk can be managed to an acceptable level to protect road users from serious harm, while helping to preserve the brand reputation of vehicle and component manufacturers,” says Martin.
The scope of cyber-security for the automotive industry is complex, challenging and ever changing and to stay on top of developments and changing threats, HORIBA MIRA also has its own self-financed research and development capability, which it uses in collaboration with a number of partners on an industry-wide level to remain in a position to be able to provide the automotive supply chain with the best advice, support and testing capability available.
According to Martin, the industry is currently in a position where it’s aware of the challenges it faces and what needs to be done but maturity levels vary in how individual organisations can respond to the challenges.
“There’s a lot of development work going on around cyber-security and it’s an exciting area for test houses,” concludes Martin
External connectivity
One company that is applying its heritage in defence and security systems to vehicle cyber resilience is Thales.
Thales has focused on the connectivity of the vehicle to the outside world. This is either provided by high speed, low latency wireless modules that transmit and/or receive data or through the vehicle’s automotive-grade embedded SIM (eSIM), which identifies itself on the network and verifies the integrity of the data it transmits. The eSIMs address the need to maintain security once the car has left the showroom using connectivity service providers and can be activated any time during its lifetime.
The eSIM enables drivers and passengers to access a variety of global in-car services, such as eCall (automatic EU emergency call in case of an accident), remote software updates and smoother recall actions.
To ensure a high degree of security, Thales supports steadfast cyber security infrastructures through strong digital authentication and encryption mechanisms. This makes it possible to protect access to the car and the data it generates or receives, send secure updates and only allow access to authorised actors during the lifetime of a vehicle. Thales Security Operation Centres (SOC) further enable car manufacturers to keep a close eye on their fleet of vehicles, secure their data and detect and respond immediately to potential cyber threats.
According to Christine Caviglioli, VP Automotive at Thales, the company has been supporting car makers in their digital transformation to build and secure connected cars for 25 years. “Today we are not only able to offer the car industry innovative connectivity systems, but also to build together the best automotive cyber-security environment, so people can trust and rely on their vehicles.”
- UK manufacturing steps up to COVID-19 crisis - April 2, 2020
- Clustering Innovation - March 12, 2020
- A Global Monitor - March 6, 2020