Hannover Messe was big on Industry 4.0 this year but the big question of how the Industrial internet of things on which it’s based remains unanswered.
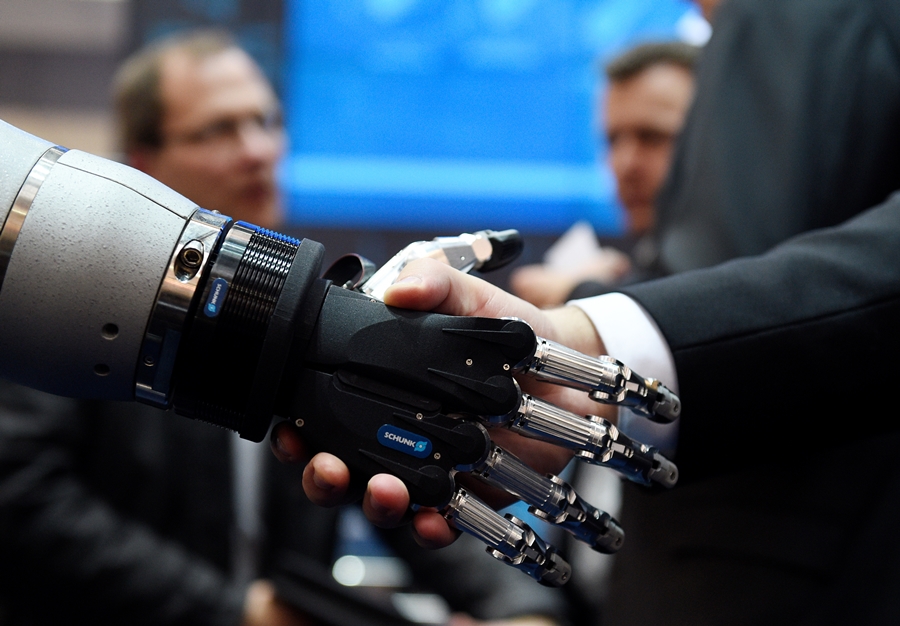
The cavernous halls of Hannover Messe were echoing with all the buzzwords surrounding digital industry; words like cobot, digitisation, Industry 4.0, IIoT and digital twin could be heard throughout the venue, regardless of the theme of each individual hall. There could be no doubt left in any visitor’s mind that the undercurrent of last year’s event was carried over in full spate to this year.
Attendees topped 225,000 representing a substantial audience for the organisers to get across their stated aim of “making the benefits of digitisation tangible”. In this respect, it was clear that there was enough innovation being showcased to keep technology enthusiasts happy and get people thinking about how the concepts of Industry 4.0 could help their businesses.
The one thing that seemed to be missing was any kind of tangible progress in securing the Industrial Internet of Things, the underlying technology that makes Industry 4.0 possible. A handful of cyber security companies were exhibiting along with the Industrial Internet Consortium, a body that exists to provide guidance and support for making sure it all hangs together operationally and securely. Each company has its own approach to offer and each could demonstrate how that approach works but nothing reached out and grabbed my attention as being much different from commercial security systems or built from the ground up to suit the needs of connected industry.
The IIoT is a complex world populated by a vast variety of devices from full-blown servers to tiny endpoints like intelligent sensors, all of which talk to each other across an equally dizzying array of communication protocols. Security systems need to recognise all these devices, understand the babble across diverse protocols, capture abnomalities and cope with connected devices which use bespoke software on unsupported operating systems. None of this will happen successfully by taking existing security software designed for commercial enterprise environments and modifying it for industrial applications. Such commercial security systems are notorious for being unreliable, rife with false positives and a drain on human resources. Such disadvantages can’t be transferred to critical industrial environments without causing severe problems.
A fresh, collaborative approach is needed that takes account of the complexity of the IIoT but is adaptive enough to stay ahead of the cyber criminals that want to gain access to it…. and at the rate the IIoT is growing, it needs to happen sooner rather than later.
- UK manufacturing steps up to COVID-19 crisis - April 2, 2020
- Clustering Innovation - March 12, 2020
- A Global Monitor - March 6, 2020